How Can Leech Protocol Offer a Safe Farming With High Profits?

Content
- What is Leech Protocol?
- Important security risks associated with DeFi projects
- How Leech Protocol manages security risks
- How Leech Protocol is unique compared to existing DeFi aggregators
What is Leech Protocol?
Leech Protocol is one of the first DeFi 2.0 automatic cross-chain yield aggregators that ensures safe farming of any cryptocurrency with effective risk management for the users. It includes different yield-farming strategies and protocols like Curve, PancakeSwap, Uniswap, etc. To maximize yield-farming and ensure safe earning, Leech Protocol introduces a unique automatic strategy to explore the capabilities of each blockchain.
For example, Leech Protocol can buy Cakes and open a double leveraged short position on 33% of the total amount and 67% put into farming with auto compound at Pancake Swap with about 80% APY. It can use any high volatility coin that can be hedged, and it’s just one strategy example. The goal is to produce high yields in interest, incentives, or additional cryptocurrency, which is the aim of yield-farming.
Leech Protocol allows yield-farmers to automatically move their funds or rewards between different blockchains in the DeFi environment. Being part of the DeFi ecosystem, the increasingly most active sector in the blockchain space, Leech Protocol runs on blockchain-based smart contracts and offers crypto investors decentralized financial services with high profits. Moreover, unlike other DeFi projects, Leech Protocol has improved on the security risks that are hindering the full potential of decentralized finance.
Important security risks associated with DeFi projects
A recent study shows that the total estimated value of locked TVL in decentralized finance protocols is $196.6 billion (as of 1/05/22) — and the higher the volume of the virtual assets DeFi accumulates, the higher the number of cyberattacks it experiences. Over the years, hacks, thefts, and frauds on DeFi have been on the rise. According to reports, DeFi users lost more than $10.5 billion to theft in 2021. By July 2021, hacks on DeFi accounted for 76% of major hacks in the crypto world, from which DeFi projects lost $361 million. This makes up a 2.7x increase from 2020. With these numbers, the importance of security of the DeFi environment could not be more clear.
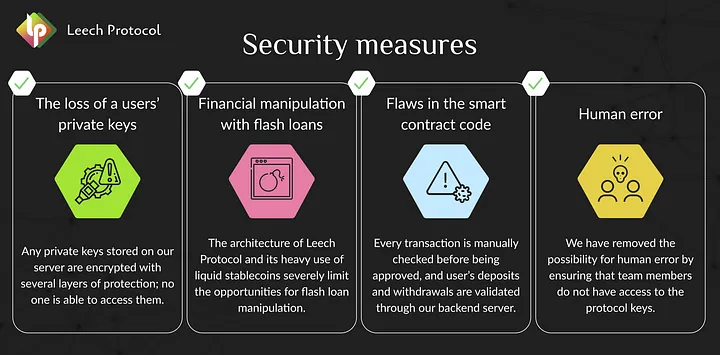
Although the contemporary DeFi environment provides easier access for underbanked people and quick settlement for the users, they are being challenged by hacks, scams, and bugs. Of course, the biggest security risks in the DeFi environment include the following: admin/private key compromise, coding mistakes, front-running attacks, flash loans, and manipulation, misuse of third-party protocols, and business logic errors. However, it is amazing how Leech Protocol is built with enough effort to ensure the safety of the DeFi environment and is certain to prevent these serious security risks while also ensuring high profit for the users.
How Leech Protocol manages security risks
Analysis of existing hacks concludes that more than a quarter of them were executed uniquely, while the rest were typical and were possible as a result of neglect of basic security rules. In effect, a seasoned team analyzed the Leech Protocol for hacks and took into account all the vulnerabilities in the protocol. The team classified all known hacks and developed possible methods of protecting against them.
Also, the team built the protocol to provide audits on each feature that affects the implementation of smart contracts as a way of tackling the security risks present in the DeFi environment. The audits will help verify smart contracts, identify errors and risks in them, evaluate and remove vulnerabilities in them, and certify them concerning a custom function specification. Besides, with the increase in DeFi projects, and considering how fast they are launched, smart contract audits will be critical to protecting the users and the community — which is why the team integrated them into Leech Protocol to give it more credibility.
Furthermore, the team incorporated a notification system in Leech Protocol to alert transactions with suspicious activity. The team intends to bring onboard white hackers to test the security system of the project. It intends to use Bug Bounty Resource Services, too. More on the security strategies that Leech Protocol will employ will be revealed in subsequent articles.
How Leech Protocol is unique compared to existing DeFi aggregators
Existing yield aggregators are plagued with various limitations that affect the profitability of users. For example, the users are unable to provide liquidity from any blockchain and are also left to choose offers from 50+ pools. Not only that, most of the users have been forced to build a complex farming system. As a result, they are actively involved in constant tracking trends on different blockchains, where they determine the most profitable strategies, calculate the associated risks, and transfer liquidity when there is a drop in profitability. This process is complex and time-consuming.
However, with Leech Protocol, the users can provide liquidity from any blockchain and get returns effortlessly. The protocol performs all the operations that the users will usually have to execute manually and determines a good Annual Percentage Yield (APY). It does this through transferring the liquidity between blockchains, searching for the best solution for the liquidity, loading the liquidity, and earning high profitability. This protocol combines farming strategies in different categories while taking into account risks and profitability.
The essence of Leech Protocol is not only to “transfer” liquidity from one blockchain to another but also to create strategies for these transfers and constantly improve them. This protocol will automatically execute multi-level strategies on different blockchains, including hedging and lending, with higher profitability. By creating strategies and automating cross-chain farming, this protocol will allow users to safely gain substantial APY and save time at the same time.
On top of that, the protocol is already in motion to create its asset insurance fund and integrate external insurance organizations. Therefore, the general public is encouraged to subscribe to the social networks of Leech Protocol to follow its development more closely.
Leech Protocol is unique in its strategies and clear in its roadmap. The cross-chain yield protocol is on track to offer safe farming in a way that will beat the imagination of yield farmers. It will not only ensure outstanding profit for the farmers and eliminate all the complexities of manual farming — but it will also save them a lot of time.
What should you do next?
- Provide liquidity via our farming App
- Follow our Twitter for more DeFi and YieldFarming tips
- Join our Telegram for Daily Farming discussion
- Join our Discord to claim your roles and become an early community member